About company
Ubiquitous Networks
Ubiquitous Networks
Military-Grade Zero Trust Protection
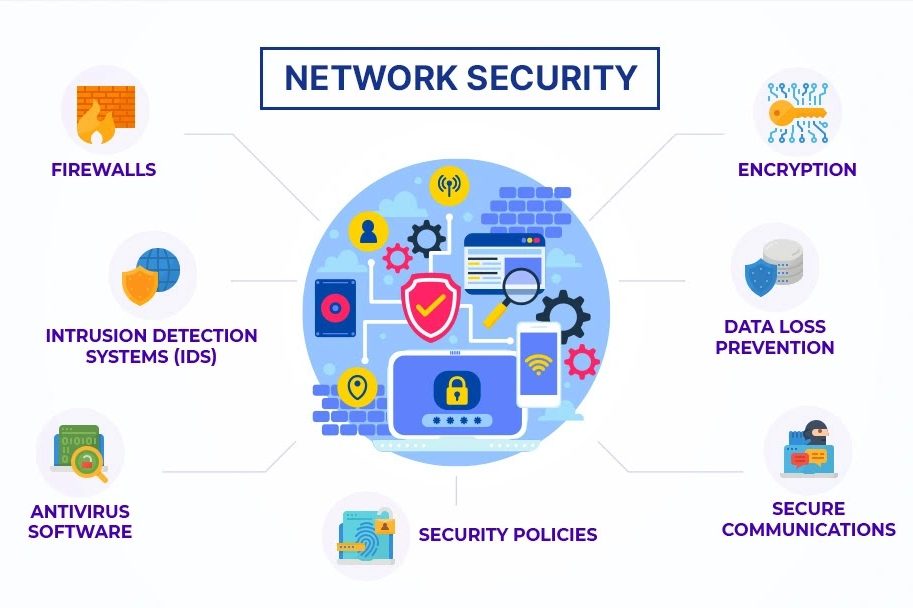
At Ubiquitous Networks, we deliver advanced cyber security and intrusion protection solutions tailored for businesses in Temecula, Riverside County, and across Southern California. With over 25 years of experience, we combine military-grade security, Zero Trust architecture, and intelligent intrusion detection/prevention to keep threats out — 24/7.
Business Problem Solving
Client Retention Rate